Information systems security plays an important role in almost every other discipline all over the world. Having said that, our security studies assignment help experts can never deny the fact that protecting information systems is a complex procedure as well. This paves the door open for new and improved security services in both domains, be it public or private. And, this is where enterprises revisit their infrastructure to satisfy the existing demands. This is the basic crux of the INFT5029 unit, which gives students an opportunity to understand the business objectives of specific organisations and support them by bringing effective security controls.
The IT revolution has transformed the working of businesses, governmental organisations, and national defense. These three functions are based on different information infrastructures. Enterprise security design and implementation become vital in protecting the data that are transmitted within different infrastructures. This helps in making all the processes run smoothly like healthcare, telecommunications, manufacturing, etc.
There are several aspects in this area that need to be covered in detail for writing high-quality INFT5029 assignments. Just like any other student, if you too feel perplexed with the concepts involved in the assignment, then you have finally reached the perfect destination. Our security studies assignment help writers are all at your service. In this blog, we will brief you on this unit and let you know we approach these assignments for the reference purpose of students. Before that, let us get straight into some of the other concepts associated with INFT5209.
5 Characteristics Of Every Enterprise Security Design
Before we discuss the enterprise security design and implementation assignment sample in detail, it will be beneficial for you to understand the characteristics of these security design systems. Just like this, there are numerous other aspects of this that cause trials for students. Fortunately, our security studies assignment help writers cover all such topics for you.
Every enterprise security design consists of:
-
Discrete security methodology
-
Unique skills and competencies set of IT architects
-
Discrete viewpoints
-
Single-purpose design components
-
Normative and Non-normative flows
To be able to approach these technical assignments with ease, it is important to gain comprehensive knowledge on all these characteristics first. Realising this, we have already done all the research for you. If you are unclear about any of these, just come to us and we will help you get an insight into these concepts to make the task a bit easier for you. This way, since 2010, our security studies assignment help experts have been “making assignments simpler” for students worldwide.
With this, we are now in a position to discuss one of our best-written INFT5029 assignment samples with you. In the last ten years, we have maintained a large storehouse of reliable samples that have come in handy to students while writing their assignments. So, you can come to us with all your questions and we will make sure that we resolve them all at the earliest.
How To Write An INFT5029 Enterprise Security Design And Implementation Assessment Answer Just Like Our Experts?
To make the approach to these technical assignments simpler, we are here with a sample for your reference. This way, we have been engaged in “making assignments simpler” for students all over the world. Without any further ado, let us get straight to the sample.
As you can see in the image below, it is the assessment brief for the enterprise security design and implementation assignment.
The main objective of this assignment is to implement Privileged identity management (PIM). There are several tasks in this assignment. Our security studies assignment help experts guide students on designing the document for the PIM, implementing the design, and more.
There are certain points that must be there in the implementation plan, which include:
-
The high-level design of the security system
-
Estimated values of the compiled costs
-
Details of the security implementation team who is engaged in preparing the plan
-
A plan that has all the components of communications and training
-
Test lab, firewall, pilot participants, and all other configuration changes that are requisite for the design
-
Execution-focused assessment of the risks and the mitigation plan for it
-
Acceptance plan
Our security studies assignment help experts include these aspects in the reference assignment solution that we draft for students all across the globe.
Now, let us share a few excerpts from the solution to this assignment that has been drafted by our experts for your reference.
This is how we begin this assignment. First, we talk about the design of the enterprise. As shown in the above image, our information technology assignment help experts begin with the context of the design. Here, we highlight the reasons why PIM used within the enterprise. This provides a brief understanding of the purpose of this assignment.
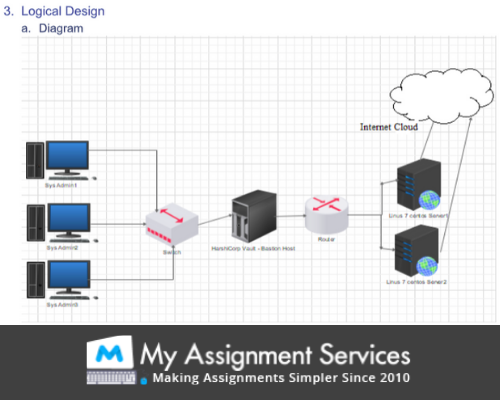
After this, we depict the logical diagram for the enterprise design as shown in the image.
At last, our security studies assignment help experts use different cases to complete the analysis of the security design.
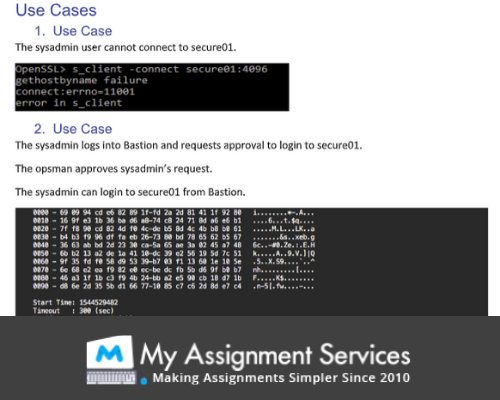
As shown in the image above, there are several cases that can be used to check the validity of the security system design. This brings us to the end of the assessment task for the INFT5029 unit. Although this is just a brief overview of the entire assignment, we have tried to cover all the crucial aspects of this assignment here for you.
If you still need our guidance on any of the aspects associated with the task, you can simply let us know of the requirements. In a few moments, we will get back to you with a complete enterprise security design and implementation assessment answer. In case you want to reach us instantly with your doubts, you can get connected to us via interactive live one-on-one sessions.
How Our Security Studies Assignment Experts Help Students In Combating All The Technicalities In These Assignments?
Having a firm command over all the concepts involved in such assessment tasks, our professional experts hold a great industry experience of more than ten years in the field of academics. My Assignment Services is a reputed organisation that takes pride in providing reliable academic assistance to students to make the assessment tasks a bit easier. We know all the nuances of writing these technical assignments, which is why we have never missed the deadlines.
We have maintained a large repository of valuable samples for our clients so that they can refer to them and clear all their doubts instantly. Other than this, our security studies assignment help experts have also come up with a wide range of added benefits for you.
Value-added Services That Are Designed For You!
Knowing the hardships that students face in these assignments, it is not enough for us to provide you with academic guidance; we completely understand the role of an assignment provider which is why we promise to fulfill all your assignment requirements. Our professional academic writers are grade-driven individuals who bifurcate each of the expectations of students and fulfill them separately.
To start with, these are some of the value-added services that we have curated for you.
-
To ensure that we provide 100% authentic work to you, we pass each of the assignment drafts through the Plagiarism software and send along a free copy for you to check.
-
Keeping an optimum price for all our assignment packages, we make it a point to never compromise with the quality of our work. To be doubly-sure that you get the utmost quality work from us, our client-satisfaction manager looks supervises the multiple quality check process and also looks into all the quality concerns to resolve them as soon as possible.
-
We have never hesitated to even make last-minute revisions for our clients. Thus, you can simply handover all the corrections that you want us to make and we will accommodate all of them and get back to you within a few moments.
-
Other than the reference assignment solutions, our security studies assignment help writers are available 24*7 via the live one-on-one sessions for you so that you can clarify all your queries instantly.
-
My Assignment Services is a storehouse of hundreds of samples for you in each of the subjects that you are studying. So, you can refer to them and begin working on your assignments easily.
Now, we have also launched a new mobile application with which you can stay updated on all our lucrative discounts and offers sitting right at your home. All you need to do is just download it and start exploring! There are several referral programs in store for you as well. With them, we provide ample opportunities for our clients to earn while learning with us. To know more about them or to place an order with us, just contact our experts today!
Related Study Materials
Our Experts can answer your Assignment questions instantly.
Ask Question0 Comment
Get It Done! Today
1,212,718Orders
4.9/5Rating
5,063Experts











Loved reading this Blog? Share your valuable thoughts in the comment section.
Add comment