A network model is regarded as the most comfortable manner of describing database objects and their connections. A network model is a domain that students encounter in their computer science courses. Its significance has made it immensely popular in the academic sector. A student pursuing a network model has to complete several academic assessments which include many technical concepts and facts. Network model assignments weigh anywhere from 20-60% of total grades but differ from university to university. It has been observed that computer science students face problems while handling network model assignments. Do you have a network model assignment pending and the deadline is close? We, at My Assignment Services, are here to provide you best-quality network model assignment help and help you pass with flying colors. Our experts are highly qualified and perfectly capable of providing quality solutions to students seeking network model assignment help online. My Assignment Services also provide IT assignment help, dissertation, thesis, essay, and so on to students in Australia, the USA, and the UK.
Our Experts Make Network Model Assignments Easier for You
A network model is a form of database model that is created as a comfortable advance towards representing objects and their relationships. Schema is a distinctive characteristic of the network model. Schema is represented as a graph where object forms are nodes and relationship forms are arcs. The schema of the network model is not limited to be a hierarchy or lattice when compared with other database models. The hierarchical trees are replaced by a graph which permits a more flexible association with the nodes.
The network model was originally developed by Charles Bachman. In 1969, the Conference on Data Systems Languages (CODASYL) Consortium created the network model into an ideal description. The objective of the network model is to share or transport information from one another end of the server. It is based upon the model of which path or route it will take to share the information from the sender to the receiver. For instance, the internet delivers its objective by posting, sharing, and transporting information or data from one end to another.
What Are the Basic Elements of a Network Model?
A network model has two basic elements. These are:
- Fields are made up of records that require a hierarchical structure.
- Sets are utilized to explain relationships such as one-to-many between records that are made up of several members and one holder.
A record often acts as a member and a holder in any sum of sets. A set is created using circular associated lists where the parent is the holder of the one record kind once in each circle. The subordinate or child is the holder of the second record kind in every circle. A hierarchical structure is built between different forms of record where X (one type) is the holder of Y (another type). Consequently, one more set can be created where the Y is the holder of the X set. In the network model, possession is explained through direction and hence, an ideal directed graph is present within all the sets.
A network model has several features as explained below.
- It can indicate redundancy in data effectively as compared to the hierarchical model.
- There are possibilities of one or more routes from a previous node to a successor node.
- The functioning of a network model is managed by confirming the organization of associated lists wherein a program sustains a standard present status and transfers one field of a record to another followed by the connections in which the record engages.
- Records are often positioned by providing standard values.
Online Assignment Help
Custom Essay Help
Dissertation Writing Service
Sneak Peek into Advantages of Network Model
- It has the simplest concept which makes the implementation easier. A deep evaluation using the other database models is given in our online network model assignment help.
- It has the potential to control several relationship types such as many-to-many, one-to-many, and one-to-one.
- It is profitable as it is easier to access the information as the data it has is effortless as compared to the hierarchical model.
- Data integrity is one of the most significant merits of the network model. This is because there is always a relationship between the child and parent segments as it is based upon the parent-child relationship.
- Data independence is more effective in network models than the hierarchical models. For a detailed essay on network model avail online network model assignment help from My Assignment Services.
Understanding Disadvantages of Network Model
- Functional Flaws: A network model requires several pointers and hence, updates, insertion, and deletion become highly complex.
- System complexity: Every record within network models has to be managed using pointers which makes the structure of databases highly complex.
- Incomplete flexibility: Although it is more comfortable than the hierarchical model, the network one still cannot meet all linkage by assigning another holder.
- Insufficient structural independence: One cannot modify a set network model structure without changing its application programs that utilize its structure to transfer the data. Hence, a modification in structure claims a modification in its use as well which causes insufficient structural independence.
Referenced Model Network
Reference models are one of the major types of network models. In computer networks, reference models provide a conceptual framework that supports standardizing the communication between heterogeneous networks. OSI model and TCP/IP protocol suite are two well-known reference models.
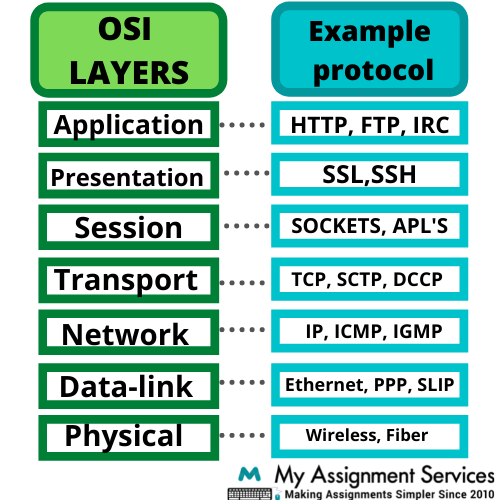
OSI Model: Internal Standards Organization invented OSI or Open System Interconnection, model. It provides a layered networking structure that designs how communication should be held between heterogeneous networks. It consists of seven interconnected layers. These are application, presentation, session layers, and so on. The diagram below represents the seven interconnected layers of the OSI model along with an example protocol.
TCP/IP Protocol Suite: TCP stands for transmission control protocol. IP stands for internet protocol. It is a chamber of protocols for communication layered in four stages. It is often utilized for communication for both private networks as well as over the internet. These four layers in TCP/IP are network access, internet, transport, and application layer.
How Network Models or Protocols Are Implemented?
Modern operating networks consist of built-in software applications that implement assistance for few network models. Software like a web browser is made up of application libraries that assist the high-level protocol required for the operation of the application or software. For TCP/IP and few lower-level routing models, assistance is implemented to enhance performance rate directly in hardware.
Every message transmitted and received over a network comprises zeroes and ones which are binary data that encode the information of every packet. Several protocols adjoin a small header at the start of every packet to gather data related to the sender of the message and its proposed location. The footer at the end of every packet is often added by a few protocols. Every network model can recognize packets of its kind and incorporate both headers as well as footers as part of transferring information over devices.
A protocol family refers to a group of network models that function together at lower and higher levels. Our network model assignment help support scholars of the IT network to learn about the OSI model.
Network Model Assignment Help Sample Provided by Our Experts
Network model is a tough subject and requires special focus on several aspects while writing an assignment. Our experts have stated various reasons why students look for network model assignment help and also, have provided a sample for you.
- A student usually has trouble understanding the basic concepts of the network model which makes it tough to write an assignment.
- Changes are inevitable in computer science and students are required to have the latest features or tools involved with the subject. Our experts know how to approach a network model assignment while using the latest changes in the subject.
- Students lack writing skills that are required to structure the assignment solution and also, are not aware of the research techniques required to evaluate relevant data.
24 X 7 Support
100+ Subjects Covered
2000+ Ph.D Experts
Why Will You Choose My Assignment Services?
Experts at My Assignment Services understand the hurdles that students face while completing their network model assignments. Our experts will support you to overcome and attain top grades by providing you with multiple features. Below are some of the perks you will get by ordering with us:
- Budget-friendly: Our experts provide network model assignment help at a student and pocket-friendly rate.
- Plagiarism-free service: Our experts will provide you a plagiarism report of your assignment solution. The report will be generated from plagiarism detecting software like Plagiarism.
- 24*7 Customer care: Our experts work tirelessly to provide you with support at any time of the day. You are free to consider our experts any time to clear all your queries and doubts regarding your network model assignment.
Get It Done! Today
1,212,718Orders
4.9/5Rating
5,063Experts
Highlights
- 21 Step Quality Check
- 2000+ Ph.D Experts
- Live Expert Sessions
- Dedicated App
- Earn while you Learn with us
- Confidentiality Agreement
- Money Back Guarantee
- Customer Feedback
Just Pay for your Assignment
Turnitin Report
$10.00Proofreading and Editing
$9.00Per PageConsultation with Expert
$35.00Per HourLive Session 1-on-1
$40.00Per 30 min.Quality Check
$25.00Total
Free- Let's Start







